wishbone offense playbook pdf
The Wishbone Offense is a run-heavy, triple-back formation emphasizing power and misdirection․ It creates a numerical advantage at the point of attack, confusing defenses with its distinctive alignment and play-action possibilities․
1․1 Historical Background and Evolution
The Wishbone Offense originated in the late 1960s, developed by coach Emory Bellard at Texas A&M․ It gained prominence in the 1970s, particularly with the University of Texas, known for its physical, run-oriented style․ The formation’s name comes from its wishbone-like shape, featuring a quarterback and three running backs․ As defenses adapted, its popularity waned by the 1980s, but it influenced modern offenses like the Option and Flexbone․ Today, it remains a nostalgic yet effective formation in football history․
1․2 Key Characteristics of the Wishbone Formation
The Wishbone Formation features a quarterback and three running backs, forming a “Y” shape․ It emphasizes power running, misdirection, and play-action passes․ The fullback and two slotbacks align behind the quarterback, creating a triple threat․ This setup forces defenses to overcommit, allowing for explosive plays․ Its simplicity and physicality make it effective for controlling the clock and dominating on the ground, while its deception keeps defenses guessing․ Playbooks highlight these core elements to maximize execution and success․

Core Elements of the Wishbone Offense
The Wishbone Offense relies on a triple-back alignment, play-action passes, and precise blocking schemes․ It emphasizes physical execution, teamwork, and deception to control the game rhythm․
2․1 Player Positions and Alignments
The Wishbone Offense features a fullback, two slotbacks, and a tailback, forming a triangle behind the fullback․ The quarterback aligns 5 yards deep, with the fullback 3-4 yards behind the center․ Slotbacks position 2-3 yards outside the tackles, creating a balanced, deceptive formation․ The offensive line, including tackles, guards, and center, must execute precise blocks to enable the rushing attack and play-action effectiveness․
2․2 Essential Plays and Strategies
The Wishbone Offense relies on the Dive, Option, and Counter plays to exploit defensive weaknesses․ The Dive Play attacks the middle, utilizing the fullback for power․ The Option Play reads the defense, allowing the quarterback to distribute the ball to the most open runner․ The Counter Play uses misdirection to reverse field and catch defenses off guard, emphasizing execution and deception to maximize yardage and control the game’s tempo effectively․

Wishbone Offense Playbook Breakdown
The Wishbone Offense Playbook outlines base plays, variations, and adjustments․ It provides a comprehensive guide to mastering the formation, focusing on execution, alignment, and strategic play variations․
3․1 Dive Play: Execution and Purpose
The Dive Play is a fundamental running play in the Wishbone Offense, designed to attack the defense’s midline․ It involves the fullback taking the handoff and aiming for the gap between the center and guard․ The play relies on precise blocking from the linemen and wingbacks to create a seam․ Its primary purpose is to establish a physical presence and control the line of scrimmage, setting up larger plays․
3․2 Option Play: Reading the Defense
The Option Play is a cornerstone of the Wishbone Offense, relying on the quarterback’s ability to read defensive alignment and movement․ The quarterback reads the linebackers and defensive ends to determine the handoff or pitch․ The play leverages the triple-back alignment to create confusion, with the quarterback either diving up the middle or pitching to the trailing back, exploiting defensive overcommitment․ This play is designed to stretch defenses and create explosive gains․
3․3 Counter Play: Misdirection and Deception
The Counter Play in the Wishbone Offense uses misdirection to deceive defenses, often involving fake handoffs and reverses․ The quarterback fakes a dive to one side while the ball is handed off in the opposite direction, creating confusion․ This play exploits defensive aggressiveness, forcing players to overcommit, and opens up large gaps for significant gains․ It is a strategic tool to counter aggressive defensive alignments․

Coaching and Teaching the Wishbone Offense
Coaching the Wishbone Offense requires emphasizing proper alignment, ball handling, and execution․ It demands repetition and drills to ensure players master the fundamentals and timing of each play․
4․1 Fundamentals for Youth Football Coaches
Teaching the Wishbone Offense to youth requires focusing on basic blocking, ball handling, and footwork․ Coaches should emphasize proper stances, handoffs, and reads․ Simplifying plays and using drills to build muscle memory helps young athletes execute effectively․ Consistent repetition ensures understanding and confidence, laying a solid foundation for more complex strategies as players progress․
4․2 Drills to Master the Formation
Drills for the Wishbone include alignment exercises, handoff gauntlet runs, and option reads․ Players practice snap counts and footwork in a controlled environment․ Coaches use tackling dummies and cones to simulate game scenarios, ensuring precise execution․ These drills reinforce teamwork and timing, helping players master the formation’s intricacies while building agility and coordination․

Defensive Strategies Against the Wishbone
Defenses counter the Wishbone by aligning in strong, gap-oriented schemes․ They emphasize quick penetration and forcing the ball inside to limit the triple-option threat effectively․
5․1 Alignments to Counter the Wishbone
Defenses must align strategically to counter the Wishbone, often stacking linebackers and safeties deep․ A nose guard occupies the center, while defensive ends contain the edges․ Aligning in heavy formations like heavy right or heavy left limits the offense’s angles and forces runs inside, neutralizing the Wishbone’s strengths․
5․2 Adjustments to Neutralize Key Plays
To neutralize Wishbone key plays, defenses must adjust linebacker depths and defensive linemen alignments․ Defensive ends should crash hard to contain option plays, while linebackers fill gaps aggressively․ Safeties provide over-the-top support to limit big plays․ Additionally, pre-snap reads and blitz packages can disrupt the offense’s rhythm, forcing quick decisions and limiting the effectiveness of dive and option plays․

Advanced Concepts and Variations
Advanced Wishbone concepts include incorporating play-action passes to exploit defensive aggression․ Modern adaptations blend traditional misdirection with contemporary RPOs and formations, enhancing versatility and unpredictability․
6․1 Incorporating Play-Action Passes
Play-action passes in the Wishbone offense exploit defensive aggression by mimicking running plays․ The quarterback fakes a handoff, freezing linebackers and safeties, creating open receivers downfield․ These plays capitalize on defensive overcommitment to the run, offering big-play potential․ Proper execution requires precise timing and convincing fakes, making them a valuable complement to the Wishbone’s ground game․
6․2 Adapting the Wishbone to Modern Football
The Wishbone offense has evolved by incorporating modern spread elements, such as RPOs (Run-Pass Options) and adjustable blocking schemes․ Coaches now blend traditional Wishbone concepts with contemporary strategies to create unpredictability․ The formation remains effective in today’s game by utilizing mobile quarterbacks and versatile skill players, allowing for dynamic play-calling while maintaining its core identity as a powerful, run-oriented attack․

Wishbone Offense Playbook PDF Resources
Discover reliable Wishbone Offense playbook PDFs online, offering detailed strategies, play diagrams, and coaching tips to master the formation and its variations for effective game execution․
7․1 Where to Find Reliable Playbooks Online
Reliable Wishbone Offense playbooks can be found on platforms like Coach’s Clipboard, FootballXOs, and select youth football forums․ These resources offer detailed diagrams, strategies, and drills․ Ensure playbooks are authored by experienced coaches and include comprehensive breakdowns of formations and plays․ Always verify reviews and previews to guarantee quality and relevance for your team’s needs․
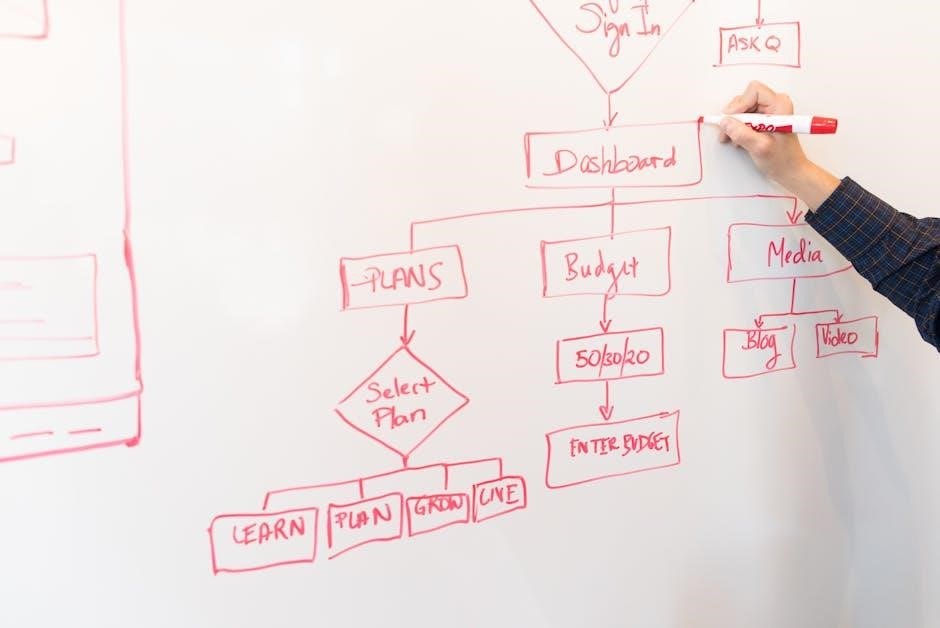
7․2 Key Features of a Comprehensive Playbook
A comprehensive Wishbone Offense playbook includes detailed play diagrams, breakdowns of formations, and strategic concepts․ It should offer clear instructions for player alignments, blocking schemes, and execution․ Look for playbooks with coaching tips, drills, and adjustments to counter defensive strategies․ Ensure it includes variations and options to adapt to different skill levels and game situations, providing a versatile toolkit for coaches․
Case Studies and Success Stories
The Wishbone Offense has proven effective in various programs, with teams achieving significant rushing yards and victories․ Its success lies in its ability to dominate ground games consistently․
8․1 Teams That Excelled with the Wishbone
The Wishbone Offense has been instrumental in the success of several prominent football programs․ Teams like the University of Oklahoma and Texas A&M famously utilized the formation to dominate ground games․ Oklahoma, under coach Barry Switzer, perfected the Wishbone in the 1970s, winning multiple championships․ Their ability to control the clock and exploit defensive weaknesses made the formation a cornerstone of their success during this era․
8․2 Coaches Who Mastered the Formation
Coaches like Barry Switzer and Emory Bellard were instrumental in perfecting the Wishbone Offense․ Switzer, at Oklahoma, leveraged the formation to win multiple championships, while Bellard, its creator, emphasized disciplined execution․ Their ability to adapt and innovate within the Wishbone framework made them legends, showcasing the formation’s potential when guided by masterful coaching and strategic play-calling․

Common Mistakes and Solutions
Improper alignment and delayed snap counts often disrupt the Wishbone Offense․ Coaches must emphasize fundamental execution and timing to ensure plays unfold effectively and efficiently․
9․1 Pitfalls in Execution
One common pitfall in executing the Wishbone Offense is improper alignment, leading to defensive mismatches․ Additionally, delayed snap counts can disrupt timing, allowing defenses to adjust․ Coaches must stress precise formation setups and rapid execution to maintain offensive rhythm and exploit defensive weaknesses effectively, ensuring each play starts with a clear advantage․
9․2 Troubleshooting Alignment Issues
Common alignment issues in the Wishbone Offense include improper backfield depth and wingback misalignment․ Coaches should ensure the fullback aligns 3-5 yards deep, with wingbacks 2-3 yards outside the tackles․ Drills focusing on pre-snap adjustments and visual cues can help correct these issues, ensuring the formation’s effectiveness and maintaining offensive balance against defensive schemes․

The Future of the Wishbone Offense
The Wishbone Offense continues to evolve, incorporating modern innovations like RPOs and play-action passes, ensuring its relevance in contemporary football by adapting to new defensive strategies․
10․1 Innovations and Trends
The Wishbone Offense is evolving by integrating modern concepts like RPOs (Run-Pass Options) and play-action passes, enhancing its effectiveness against contemporary defenses․ Coaches are adapting the formation to fit today’s fast-paced games while maintaining its core power-running identity․ Innovations include leveraging spread concepts and motion adjustments to create mismatches, ensuring the Wishbone remains a dynamic and formidable offensive strategy in modern football․
10․2 Its Place in Contemporary Football
The Wishbone Offense remains a strategic option in modern football, valued for its ability to control the clock and dominate on the ground․ While less prevalent at higher levels, it thrives in youth and smaller college programs due to its simplicity and physicality․ Its emphasis on execution and discipline makes it a timeless choice for teams seeking a powerful, run-oriented identity in today’s game․
The Wishbone Offense remains a potent, run-focused system, emphasizing execution and physicality․ Its adaptability and simplicity make it a timeless choice for teams seeking a strong ground game․
11․1 Summary of Key Points
The Wishbone Offense is a run-oriented system with a triple-back alignment, emphasizing misdirection and physical execution․ Its simplicity and adaptability make it effective at all levels of play․ Key elements include the dive, option, and counter plays, requiring precise timing and discipline․ Coaches must focus on fundamentals, drills, and player positioning to maximize its potential․ The Wishbone remains a powerful tool for teams seeking a strong ground game․
11․2 Final Thoughts on the Wishbone Offense
The Wishbone Offense remains a timeless and effective system, particularly for teams emphasizing a strong ground game․ Its simplicity and adaptability make it ideal for youth football while still offering complexity for advanced play․ Coaches who master its fundamentals can unlock consistent success․ The Wishbone’s focus on execution, discipline, and misdirection ensures its relevance in modern football, making it a valuable playbook addition for any program․

Additional Resources and Further Reading
Explore Wishbone Offense playbooks, eBooks, and coaching guides online․Join football forums and communities for shared strategies and expert insights to enhance your playbook knowledge and execution skills․
12․1 Recommended Books and Articles
Essential books include “Wishbone Option Series” and “The Best Youth Football Plays,” offering detailed strategies․ Articles like “Mastering the Wishbone Formation” provide insights into execution and drills․ Resources by experienced coaches and analysts are available online, covering playbook designs, drills, and game strategies to enhance your understanding and implementation of the Wishbone Offense effectively at all levels of play․
12․2 Online Communities and Forums
Online forums like Reddit’s r/footballcoaching and specialized coaching websites offer valuable discussions on the Wishbone Offense․ Communities such as Coach’s Corner and Football Strategy Forum provide insights, shared playbooks, and advice from experienced coaches․ These platforms allow for interaction with experts, access to video tutorials, and downloadable resources, making them indispensable for mastering the Wishbone Offense playbook effectively․